Coder v1.14: Container-Based Virtual Machines, Account Dormancy, Environment Variables
We’re pleased to announce the release of Coder v1.14.0!
This release includes new features like the ability to run system-level applications in your environments, account dormancy, environment variables, UI improvements, security updates, and bug fixes.
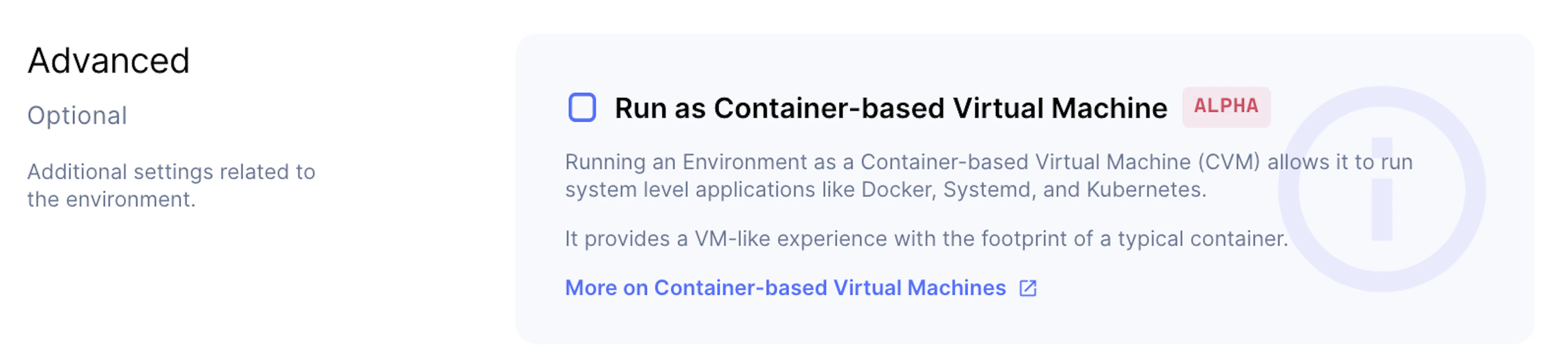
Container-Based Virtual Machines (CVMs)
Coder now allows you to create environments capable of running system-level applications like Docker, Docker Compose, Kubernetes, or systemd. We call this variant of our standard environment a Container-based Virtual Machine. When you choose this option, your environments behave like virtual machines with all of the image, security, and performance properties of typical containers.
Account Dormancy
Coder now flags accounts that haven’t been used in 90 days as dormant. Dormant accounts do not count toward your license seats.
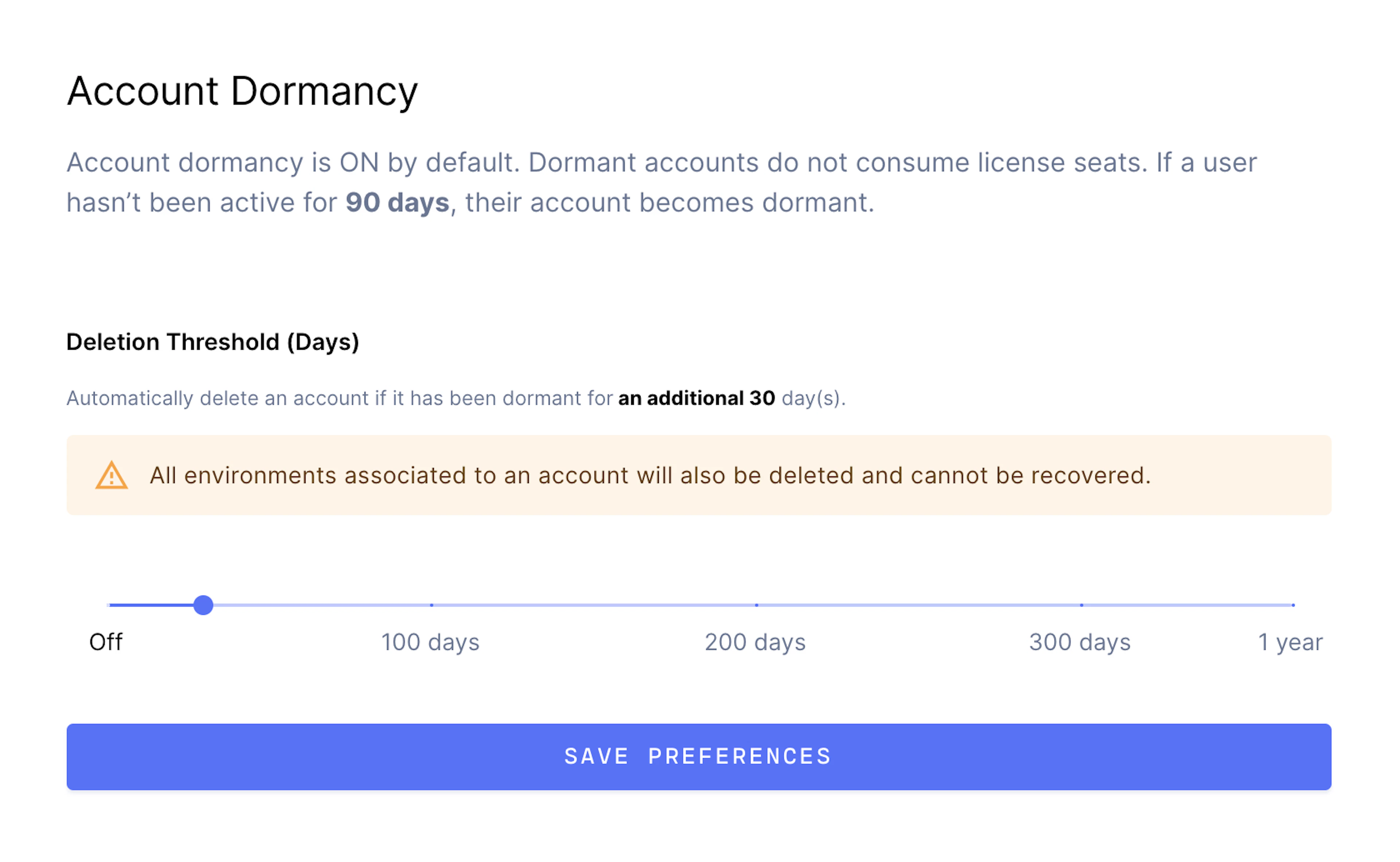
You can also set a deletion threshold. After this threshold, Coder will automatically delete dormant accounts (e.g. if you set a deletion threshold of 30 days, Coder will delete accounts that haven’t been used in 120 days).
Coder Environment Variables
Coder injects a standard set of environment variables that allow you to access contextual information about your Coder environment.

UI Improvements
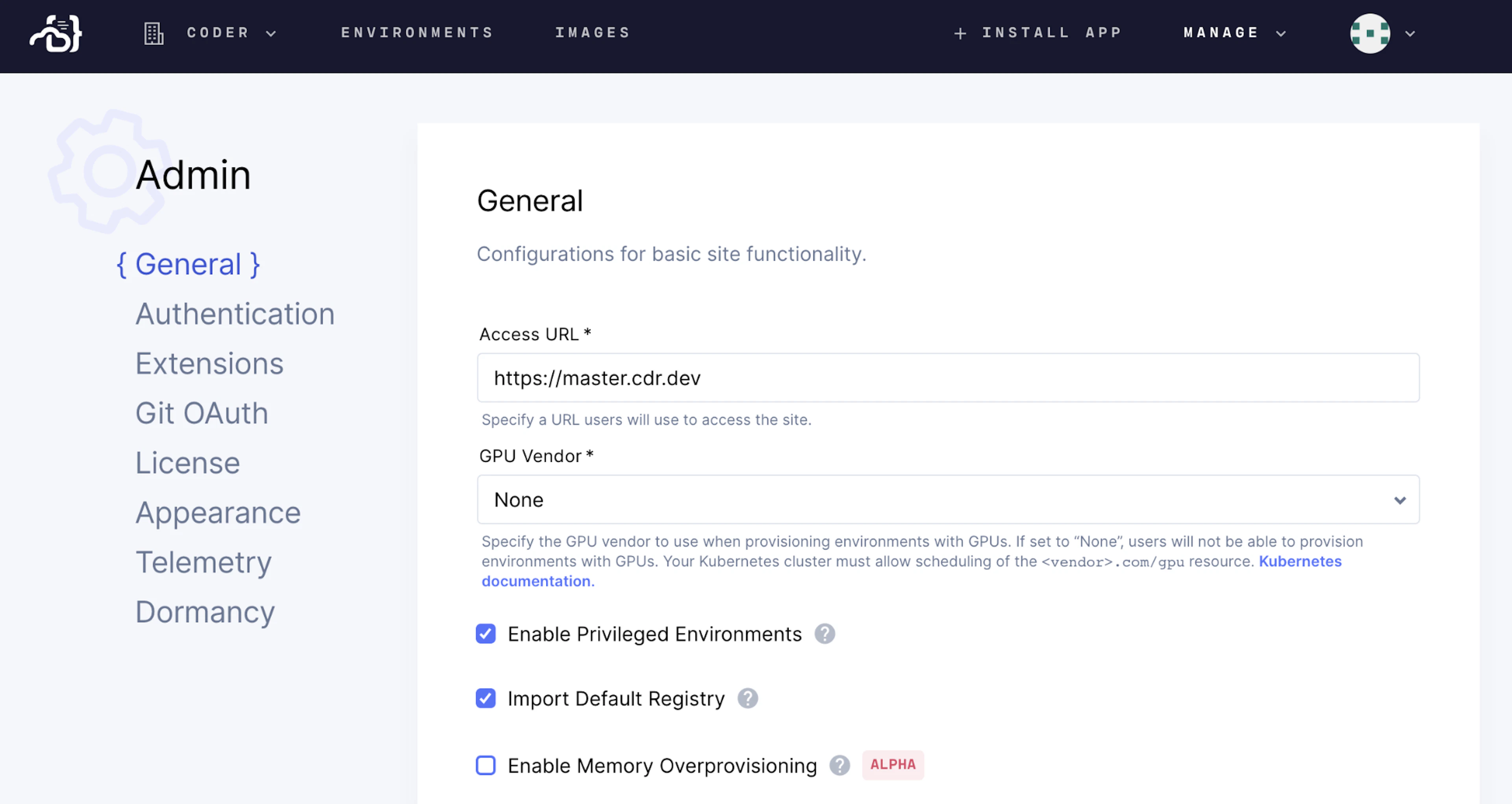
Admin-level users (such as site managers) will notice that we’ve redesigned all of the Admin pages.
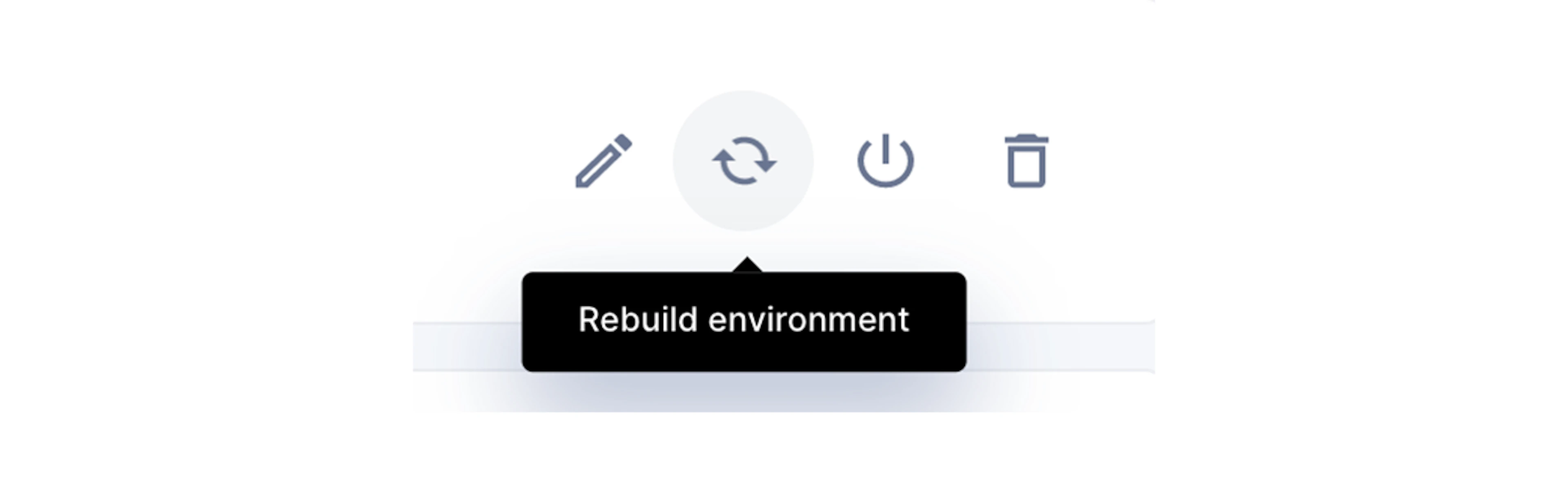
We’ve also redesigned the toggles in the Coder UI, the Progressive Web App icon, and the Rebuild Environment icon.
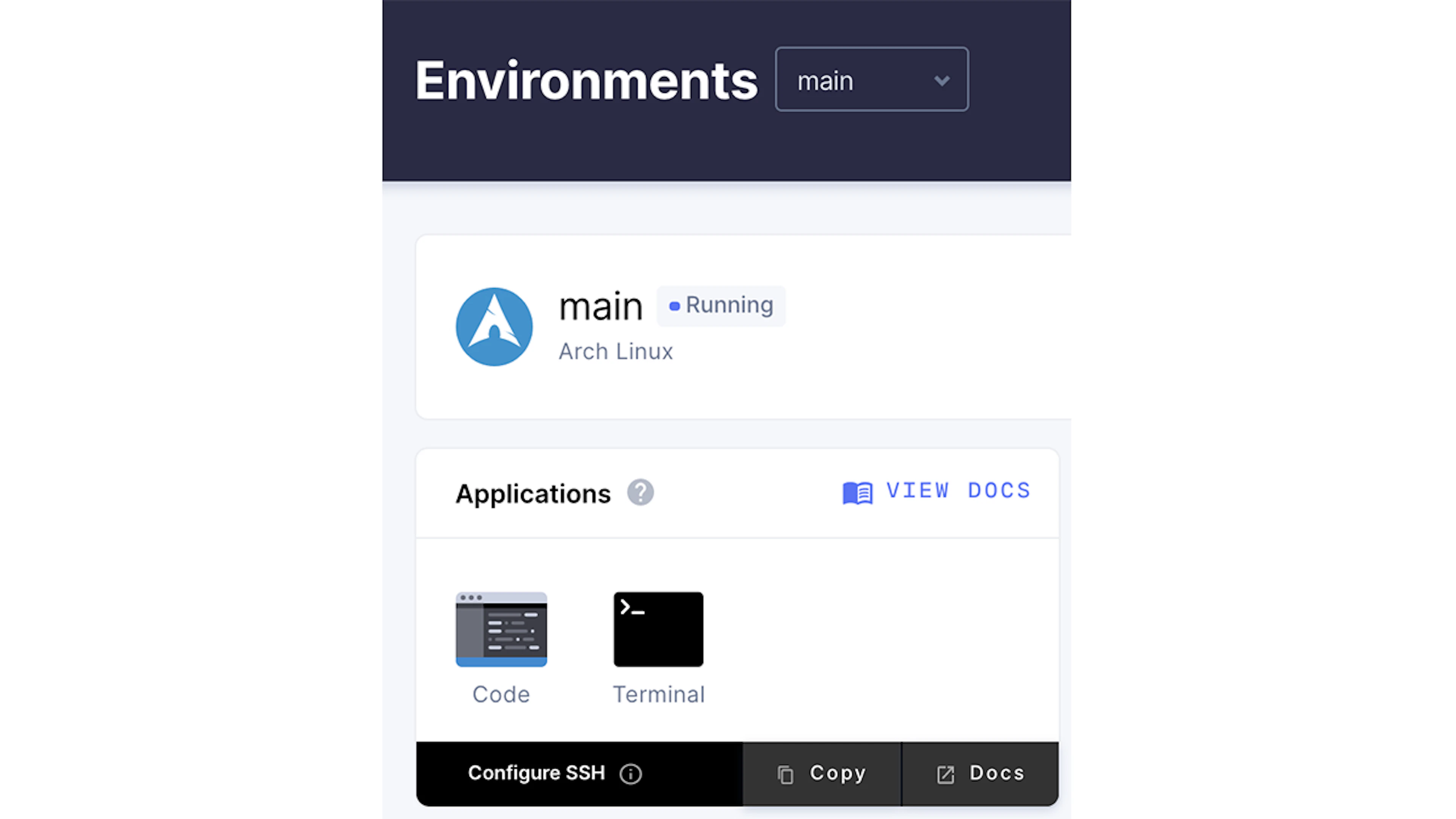
Other UI changes include the displaying of SSH information (as well as links to educational material) on the environment overview page and improved code blocks.
Security Updates, Bug Fixes, and Other Under-the-Hood Improvements
We’ve enhanced security around the use of API keys within your environments and fixed an upstream SSH server DoS vulnerability.
Subscribe to our newsletter
Want to stay up to date on all things Coder? Subscribe to our monthly newsletter for the latest articles, workshops, events, and announcements.




