
Team-owned workspaces and AI governance in 2.32
Give every builder the right access, the right tools, and a full audit trail without credential chaos. Learn more in our blog post.
Collaborate inside workspaces with Shared Workspaces
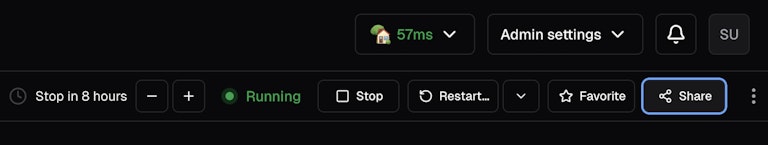
Getting another person into a running workspace used to mean credential sharing or building custom tooling. Now workspace owners can grant access to specific users, groups, or organizations. Available in Coder open source.
- Auditable access: Administrators can see who accessed a shared workspace and when.
- Credentials are protected: A shared workspace authenticates to external systems as the service account, not as an individual person.
- Easy authentication: Users leverage their own Coder credentials and get full access to the same files, tools, services, and running processes
Service Accounts GA
Service Accounts let teams own environments under a non-human identity. Common use cases include on-call troubleshooting, QA and preview environments, scale testing, and shared ML training boxes. Available in Coder Premium.
- Safer access: Any engineer on rotation can jump into a pre-configured workspace immediately without sharing credentials or waiting for the owner to come online.
- Persistent team environments: Service-account-owned workspaces survive employee departures and team changes, keeping environment state and data intact.
- Policy controls are built in: Restrict sharing to service-account-owned workspaces only to block peer-to-peer sharing, which carries more risk in compliance-sensitive deployments.
Learn more in our documentation.
Coder AI Governance Naming Update
We’ve renamed two features to make them clearer and more intuitive: AI Bridge is now AI Gateway, and Agent Boundaries is now Agent Firewall. There are no changes to functionality. Both capabilities remain part of the Coder AI Governance solution, with documentation updates in progress.
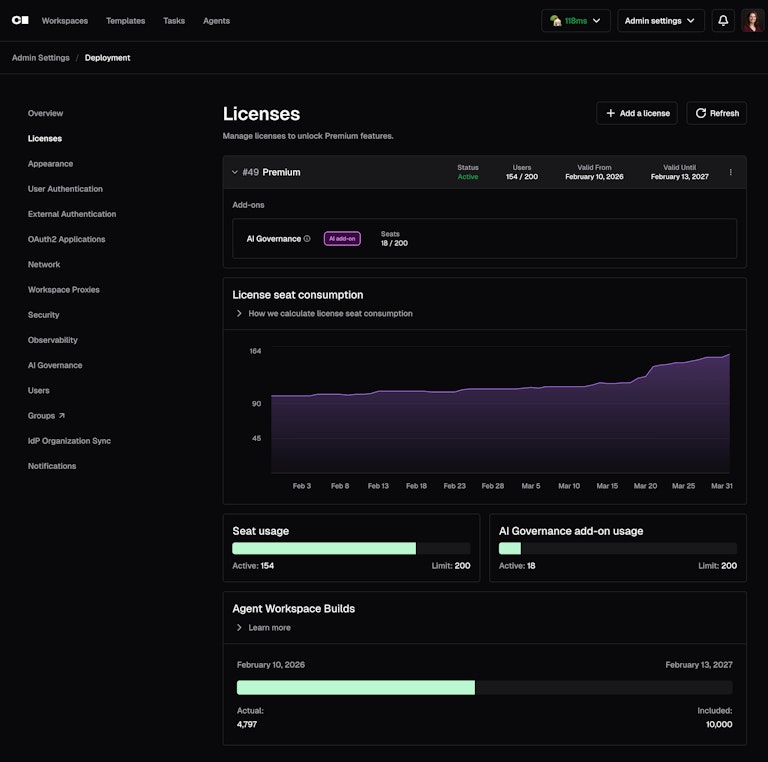
Usage controls, session tracking, and BYOK support in the Coder AI Governance Add-On
Release 2.32 adds additional enterprise-grade controls and observability over AI usage.
- Controlled rollout: Control AI access by user and enforce per-user agent workspace build quotas to prevent a single user from exhausting shared deployment capacity. Learn more here.
- Bring your own key (BYOK): Developers can bring their own LLM provider keys without bypassing governance, maintaining authentication, policy enforcement, and full observability of all requests. Learn more here.
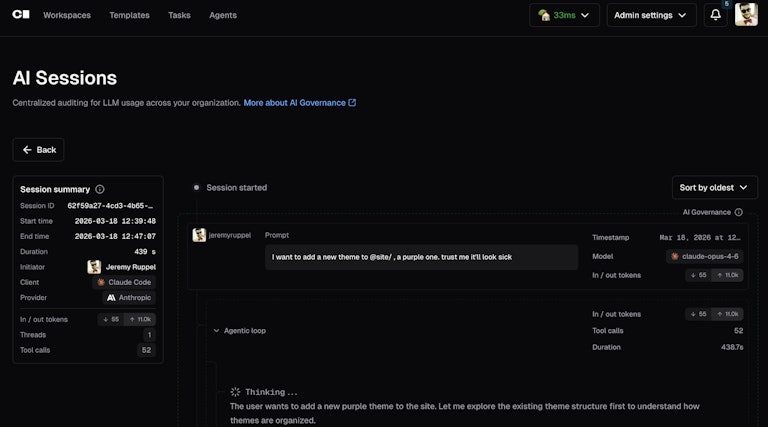
- End-to-end visibility: Understand how and why AI actions occur by correlating interactions into sessions when available, linking prompts, reasoning, and tool invocations into a causal chain. Learn more here.
Breaking Changes
- #23031: Injected MCP tools are now deprecated in AI Gateway; this feature will remain functional but will be replaced with an MCP Gateway in a future release.
- #23320: Regular users without auditor or admin roles can no longer view AI Bridge Interceptions.
View the full changelog on GitHub. If you have questions or feedback, join the conversation on Discord or email us directly!



